Each one of the pictures is offered a singular numerical variety referred to as a hash. Google then scans Gmail in search of the special hashes. When suspicious images can be found Google reports the incident to the right nationwide authorities.[109] HeritageAs with every new technologies, use scenarios must drive zero-have faith in adoption choice
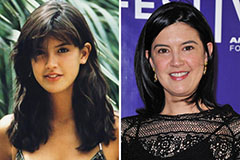 Phoebe Cates Then & Now!
Phoebe Cates Then & Now! Atticus Shaffer Then & Now!
Atticus Shaffer Then & Now! Katey Sagal Then & Now!
Katey Sagal Then & Now! Morgan Fairchild Then & Now!
Morgan Fairchild Then & Now! Naomi Grossman Then & Now!
Naomi Grossman Then & Now!